If you think, your office is secured because it’s on the top floor of a skyscraper building, then you may need to rethink as in this day and age, pretty much nothing is unhackable—not even office printers locked at the top floor.
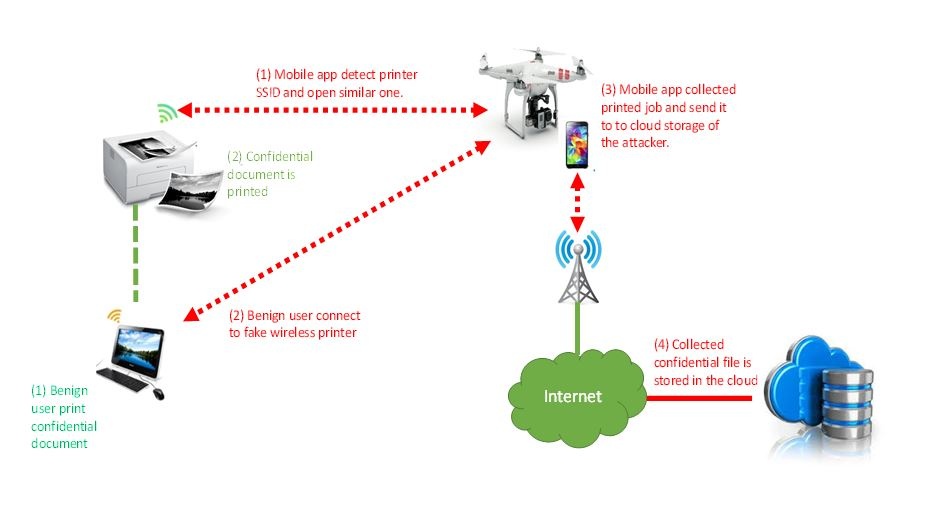
Yes! A group of security researchers from Singapore has built a drone that along with a smartphone and custom applications can be used to automatically steal documents from printers with open Wi-Fi connections. The technology was developed by researchers from iTrust, a cyber security research center at the Singapore University of Technology and Design.
The researchers used a standard drone from a Chinese firm, DJI and used it to transport a Samsung Smartphone to an area where a wireless network with wireless printer was located.
The researchers used two applications that they developed:
▬The first app establishes a bogus access point once the open wireless printer is detected. The access point mimics the printer and tricks computers in the internal wireless network to send sensitive documents to it.
▬The second app is Cyber security Patrol, which is designed to scan the air searching for open Wi-Fi printers and automatically notify the organization’s IT department. This app has been designed to improve the security of the target organization. It looks for unsecured printers in the target organization accessible via the drone, but rather launching the attack, it took photos of the compromised printers and reports it to the internal staff.
Once a document is intercepted, the app can send it to an attacker’s Dropbox account using the phone’s 3G or 4G connection, and also send it on to the real printer so a victim wouldn’t notice the hack.
The attack zone is limited to 26 meters in radius. But with dedicated hardware, an attacker could generate a stronger signal which can extend that range further. Any computer inside the attack zone will opt to connect to the fake printer over the real one, even if the real printer is closer in proximity to the rogue one.
A drone hovering outside an office building would be obviously spotted, but the goal of the project intended to help companies so that they could be taught how easily accessible Wi-fi printers can be which can be stolen by hackers to steal data or get into their networks.
The project was part of a government-sponsored cyber security defense project.
Student researchers Jinghui Toh and Hatib Muhammad developed the method under the guidance of Professor Yuval Elovici of Department of Information Systems Engineering at Ben-Gurion University of the Negev.
The system targets wireless printers because wireless printers are supplied with the Wi-Fi connection open by default, and many companies forget to close this hole when they add the device to their Wi-Fi networks. This open connection potentially provides an access point for outsiders to connect to a network and steal a company’s sensitive data.
The researchers also demonstrated that the attack could also be carried out by hiding a cellphone inside an autonomous vaccum cleaner, after which the device will continuously scan for organisation’s networks for printers with unsecured connections.
The project conducted by the researchers demonstrated once again the close link between physical and logical security.
Any person can simply install the Cybersecurity Patrol app on a smartphone and attach it to a drone to and send it upwards. Though the same method can be used by organizations to check for unsecured printers and other wireless devices.
It’s true that every invention and development comes with both pros and cons but if the cons have greater risk, then it’s time to approach physical security in a different way.
——–myabhya——–
(Perfect Training Center)

Nice think sir
LikeLike
thank you
LikeLike